What is a ‘hybrid’ threat?
Jérôme Clech. In addition to states that practice hybrid warfare (such as Russia or China), combining conventional modes of action and information manipulation (fake news, deep fakes, etc.), the hybrids; criminals, traffickers, gangsters and terrorists, use the same technological means that enable globalisation. They make up its dark side, which is why they represent such a challenge for states and even large companies.
IT has not put an end to the asymmetry of hard power between developed states and non-state actors, but it does serve an equaliser in all areas of soft power closely linked to the informational sphere (culture, influence, media, social networks, propaganda, etc.). As information moves at the speed of light for everyone. By investing in the “infosphere”, non-state actors have restored the symmetrical aspect of confrontation, but in a mainly non-kinetic register: the impact of an attack is much greater than the number of deaths, as Western societies have a very low acceptance of risk.
How can we respond to this threat?
Hybrid threats require a hybrid strategy. Our national defence and security strategy, considering the absence of a “critical mass” in our system, aims to lower the trigger point for large-scale military intervention, particularly in the event of hybrid attacks. But there is a gap in the continuum of strategic functions that neither nuclear “deterrence” nor the “protection” of territories and populations can fill. A form of “augmented prevention” would be required: the current “prevention” would be extended to in-depth action aimed at intimidation and early disruption through a combination of remote kinetic strikes and cyber offensives, not only in the physical layer of cyberspace, but also in the logical and socio-cognitive layers of cyberspace.
In concrete terms, augmented prevention would focus on nerve points, such as drone strikes aiming to neutralising terrorist leaders, for example. Both military and largely dehumanised and – more or less – stealthy or scheduled, these remote strikes are also the source of ethical concerns. Europe is following suit, since one of the projects of the Permanent Structured Cooperation (PESCO, established in 2017) is none other than the MALE (Medium Altitude Long Endurance) Eurodrone, which could eventually be armed and whose development is partly financed by the precursor of the European Defence Fund (EDF).
On the cyber side, cyber offensives constitute a hybrid mode of action at a distance: with a material aim when it is a question of hitting the physical layer of cyberspace; immaterial when it is a question of exploiting or reaching the infosphere. A Computer Network Attack (CNA), which is hybrid in nature in that it involves internalising hacking skills within the defence establishment, is a cyber offensive mode acting on the logical layer. Hybrid and cyber threats are one of the areas of NATO-EU cooperation, and PESCO has nearly ten projects in this area.
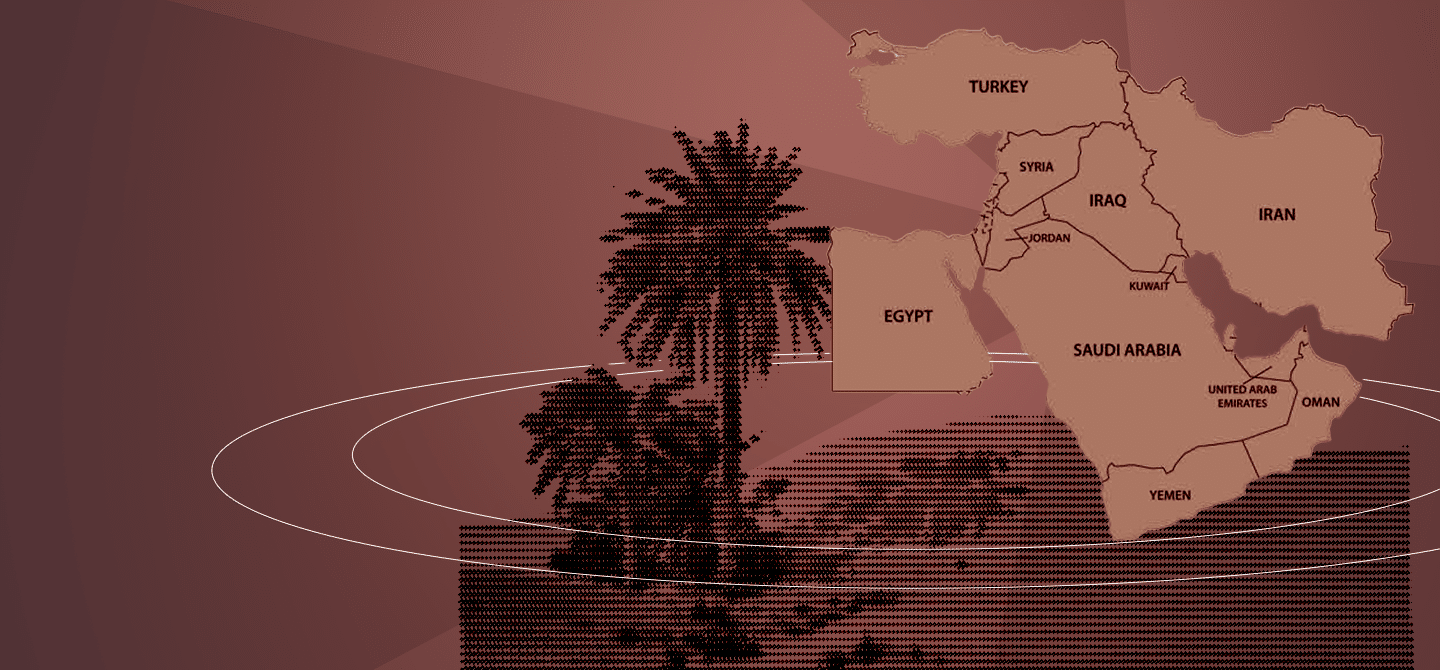
Augmented prevention could also have an impact through hybrid border surveillance. Drones are a great asset in terms of observation and are used in the civilian sector for border surveillance in the United States. The aim is not only to hinder illegal immigration, which is known to feed into every level of the illegal economy, but also trafficking of all kinds (arms, drugs, counterfeit goods, etc.), which hybridises the threats and provides a breeding ground for international terrorism. Since 2020, the use of drones has strengthened the Frontex system at the borders of the European Union (EU). Integrating the system into the range of sensors operated by the intelligence community (including the DGSE and Tracfin) would undoubtedly increase its effectiveness.
The aim is to characterise and identify the potential threat posed by an individual according to their behavioural profile.
From border control to border risk management, the emergence of the concept of “smart borders” corresponds to the implementation of “intelligent” systems at airports, initially based on biometrics. The aim is to characterise and identify the potential threat posed by an individual according to their behavioural profile. For example, the PNR (Personal Name Record) is a device for assessing the risk of a traveller being linked to a terrorist organisation; it is designed to know “what the individual has done” before booking a flight and to predict “what he or she is likely to do” at destination.
In order to see more clearly into the digital maze generated by the “computerisation of the body” (the shadow body, a cloud of data and information that goes beyond one particular individual since some of this data only makes sense as part of a series), it could then be useful for the datamining enabled by AI to cross-reference the PNR with the files held by national defence and security forces, and more particularly those held by agencies in the intelligence community. Subject to network sovereignty in place at a European level (as this is the relevant scale), it is conceivable that all this data could eventually be hosted on a dedicated cloud.
But what would be the value of a secret cloud if only France was to input in certain elements of the intelligence information collected by its sensors (relating to counterterrorism or illicit flows, for example)? For the time being, we only have an Intelligence College in Europe – not a European College of Intelligence! Naming it such might bring it to life, or perhaps not: nothing operational, but the ambition to build a “common strategic culture” … This, as Jean Monnet believed, is certainly where any European project should start, but considerable efforts need to be made, as President Macron acknowledged in his 2017 Sorbonne speech with the European Intervention Initiative (EII).
Naturally, the use of data and the search for such synergies raise ethical and legal questions that bring us back to the security-freedom dilemma.
Are we heading for widespread hybridisation?
The response to hybrids would in fact benefit from more hybridisation. For while technologies have a major and growing role to play, the related capacities (equipment and know-how) must not be reduced to technical fetishism. We must be able to articulate the exploratory force of the machine with human intuition in order to, at least, strengthen their co-production if not hybridise them. Augmented prevention would only be a strategic shift. We need to do even more: a quantum leap in terms of the anticipation of threats. Anticipating hybrids so as not to have to respond to them is, in my opinion, the way to understand the logic of “winning the war before the war”, to quote the Chief of Staff of the Armed Forces. This would imply rethinking the methods and tools of strategic foresight, paying renewed attention to the early detection of “weak signals”, in order to nip future threats in the bud before they emerge. Perceiving and characterising the underlying structure of emerging hybrid phenomena undoubtedly requires defining and building the ‘honest cyborg’ of the 21st century. But that’s another story!